Table of Contents
- Introduction to Google Home Being a Security Risk
- How Google Home Works
- Potential Security Risks
- Minimizing Security Risks
- Conclusion
- Frequently Asked Questions
Introduction to Google Home Being a Security Risk
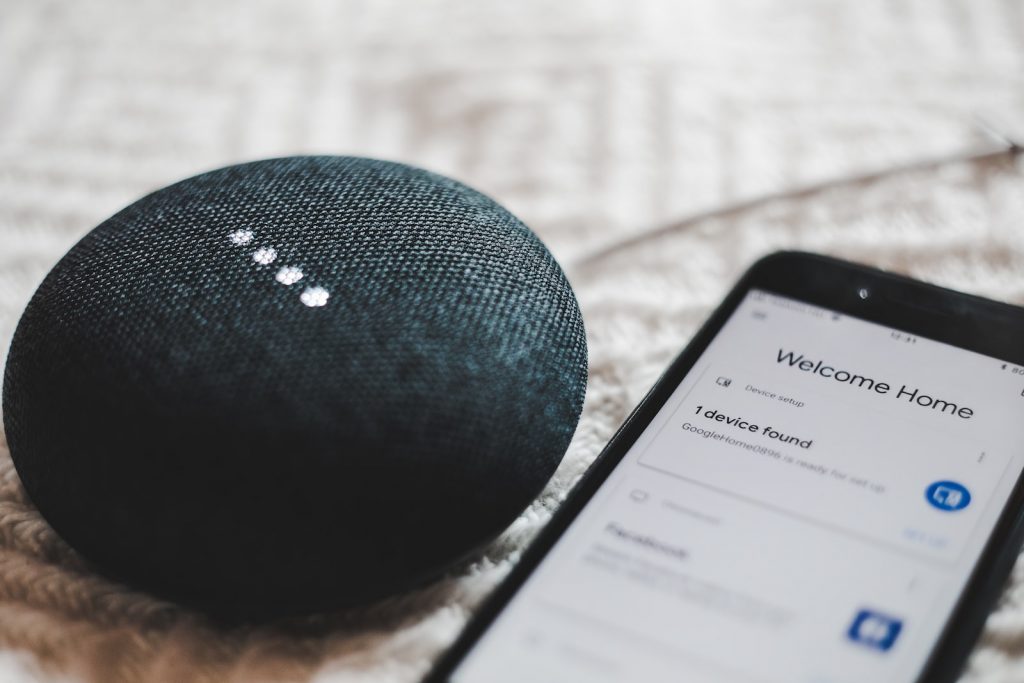
Google Home is a versatile device that can greatly enhance your daily activities. With its built-in Google Assistant, it can listen and understand queries posed in natural language, allowing users to easily access its many features.
From music playback to delivering news briefings, Google Home has almost no limit to what it can do. Moreover, its integration with various smart home devices allows users to control items throughout the home, such as lighting or thermostats.
Furthermore, because of its continued development and updates, its list of services only keeps growing for those who own a Google Home device. With such limitless potential and convenience, owning a Google Home could quickly become an integral part of one’s lifestyle without breaking the bank.
While Google Home offers a wide range of convenient features, there are also some concerns about its security.
In this blog post, we’ll take a closer look at the potential security risks associated with Google Home and provide some tips for minimizing those risks. We’ll start by explaining how Google Home works, including how it collects and uses data.
Then, we’ll delve into the different types of security risks that have been identified with Google Home, including specific examples of security breaches or vulnerabilities. Finally, we’ll provide some practical advice for securing your Google Home device and protecting your personal information and network security.
By the end of this post, you’ll have a better understanding of the potential security risks associated with Google Home and know what steps you can take to protect yourself.
How Google Home Works
In order to fully understand the potential security risks associated with Google Home, it’s important to first understand how the device works.
Google Home is a voice-controlled smart speaker that allows users to interact with their home and other devices through the use of voice commands. The device uses Google Assistant, which is powered by Google’s AI technology, to interpret and respond to the user’s commands.
One of the main features of Google Home is its ability to collect and use data. As you interact with the device, it collects information about your preferences and habits, such as the music you listen to, the news you like to hear, and the devices you control.
This information is then used to personalize your experience and provide you with more relevant information and suggestions. While this may be convenient, it also raises concerns about privacy and security.
Another feature of Google Home is that it can be controlled remotely. As Google Home is connected to the internet, it can be controlled from anywhere.
This means that if someone gains access to your Google Home device, they can use it to control your smart home devices, play music, make phone calls, and access your personal information.
Potential Security Risks
The potential security risks associated with Google Home can vary widely, from data breaches to unauthorized access to your smart home devices.
One of the most common concerns is the risk of data breaches, in which an attacker gains unauthorized access to your personal information.
This could include sensitive information such as your home address, phone number, and even credit card information. This could be especially concerning if you use Google Home to make online purchases or to access your financial information.
Another potential security risk is the possibility of unauthorized access to your smart home devices.
As Google Home can be used to control other connected devices in your home, such as lights, thermostats, and security cameras, if someone gains access to your Google Home device, they could also gain access to these other devices. This could potentially allow them to change settings, view footage, or even turn off your security system, leaving your home vulnerable to intrusion.
It’s also worth noting that Google Home is not immune to hacking. Researchers have demonstrated the ability to hack Google Home devices and use them to record audio, access personal information, and even control other devices. This highlights the importance of keeping your Google Home device and network security updated and protecting your personal information.
Lastly, there is also a concern about Google’s privacy policies. Google Home collects data from every interaction and uses it to improve the user experience, but this also means that Google has access to this data, and they can use it for other purposes.
This could include targeted advertising, data analysis, or even sharing it with third parties. While Google has stated that they are committed to user privacy, it’s still important to be aware of the privacy policies and take steps to control the data that Google Home collects.
Minimizing Security Risks
Now that we’ve examined the potential security risks associated with Google Home, let’s turn our attention to the steps you can take to minimize those risks.
The first and most important step is to secure your Google Home device and network. This includes setting up a strong and unique password for your device, as well as keeping your device and network security updated with the latest security patches and software updates.
Another important step is to control the data that Google Home collects. This can be done by adjusting the privacy settings on your device and limiting the information you share with the device.
For example, you can choose not to share your location information or personal contacts with the device. Additionally, it’s important to be mindful of the commands you give your device and the information you share.
Another important step to protect your Google Home device is to use the two-factor authentication feature. This feature requires a user to enter a verification code sent to their phone or email after entering their password, adding an extra layer of security to your device.
You can also disable or restrict access to certain features of the device. For example, you can disable the option that allows your Google Home to make phone calls or send messages.
If you’re concerned about the device being controlled remotely, you can also enable the guest mode feature which will limit the functionality of the device when it is not in use.
Lastly, it is also important to be aware of the potential phishing attempts to gain access to your device. Scammers may try to trick you into sharing your personal information or login credentials, so it’s important to be vigilant and not click on any suspicious links or give out any personal information.
By following these steps, you can minimize the potential security risks associated with Google Home and protect your personal information and home security.
Conclusion
In conclusion, it’s clear that while Google Home offers a wide range of convenient features, there are also some potential security risks associated with the device. We’ve examined these risks in detail, starting with an overview of how Google Home works and how it collects and uses data.
We’ve also delved into the different types of security risks that have been identified with Google Home, including data breaches, unauthorized access to smart home devices, hacking, and privacy concerns. Finally, we’ve provided some practical advice for securing your Google Home device and protecting your personal information and network security.
By following the tips and recommendations outlined in this blog post, you can minimize the potential security risks associated with Google Home and enjoy the convenience and benefits of this device with peace of mind.
Frequently Asked Questions
Google Home is a voice-activated assistant device that enables users to control their environment with voice commands. It can be used to play music, adjust thermostats and smart lights, place online orders, and more.
Google Home has a wide range of features, including voice commands, multi-room audio setup, access to Google services and products, integration with compatible devices like Chromecast, compatibility with smart home systems like Nest and Philips Hue, and more.
Google Home, like any other internet-connected device, can pose security risks if not properly secured and configured. However, with appropriate security measures in place and being aware of potential risks, the risk can be minimized.
Google Home is a voice-controlled smart speaker that uses Google Assistant, which is powered by Google’s AI technology, to interpret and respond to the user’s commands.
The benefits of using Google Home include convenience, control over the environment, integration with compatible devices and services, access to Google products and services, advanced automation features, and more.
Yes, Google Home collects information about your preferences and habits, such as the music you listen to, the news you like to hear, and the devices you control, and shares it with Google, which could raise concerns about privacy.
Tips include securing your device with strong and unique passwords, adjusting privacy settings, disabling or restricting access to certain features, and being aware of potential phishing attempts.
Tricks include using Google Home as an alarm clock, creating custom routines, and controlling other smart devices with Google Home.







